Impersonation Detection
Last updated: October 14, 2025
HackerRank helps detect impersonation during a test and offers the following features for impersonation detection:
Features that do not use AI to detect impersonation:
Photo Identification
Image Proctoring
Multiple Monitor Detection
Webcam Switch Detection
Photo Identification
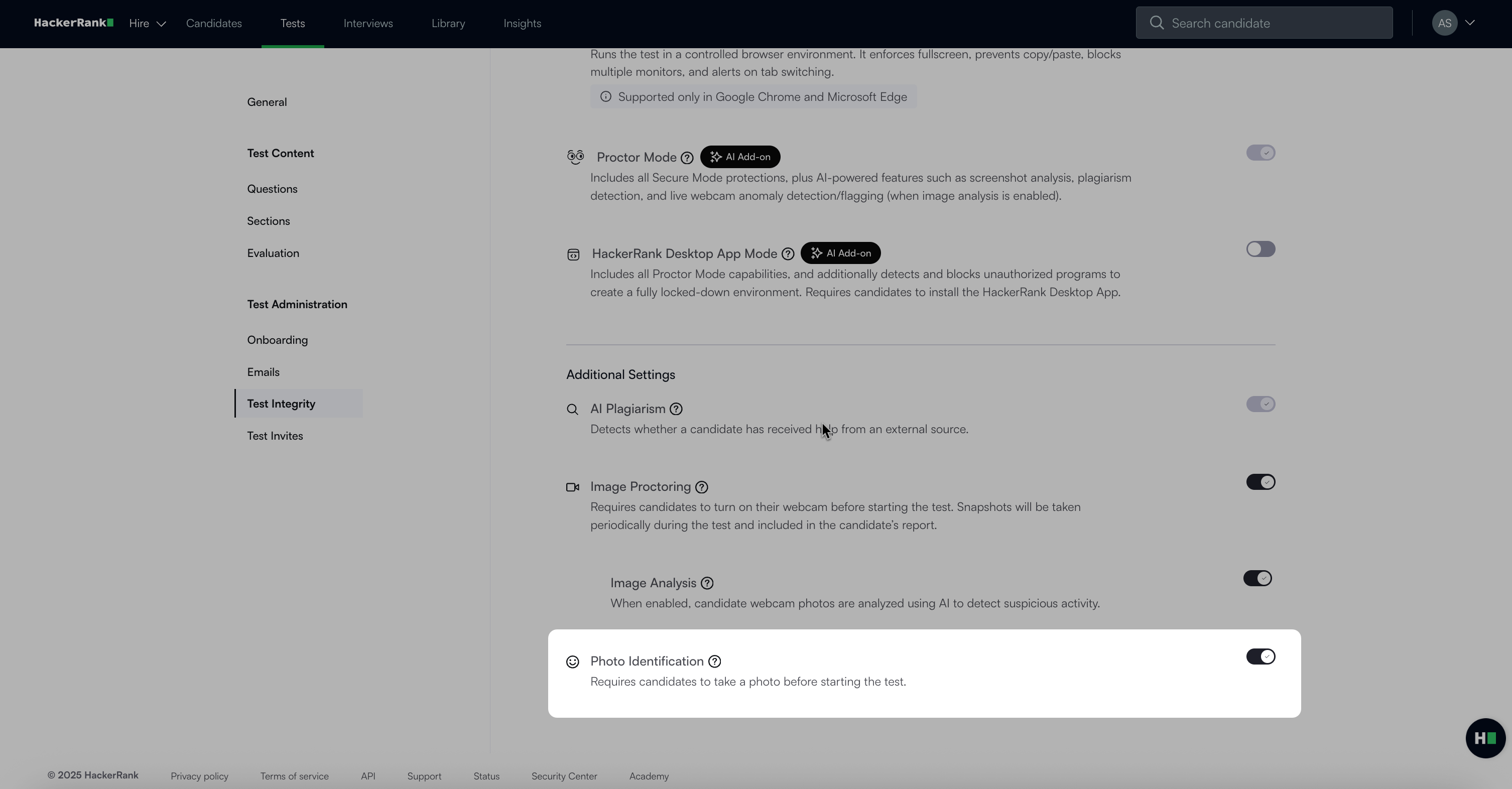
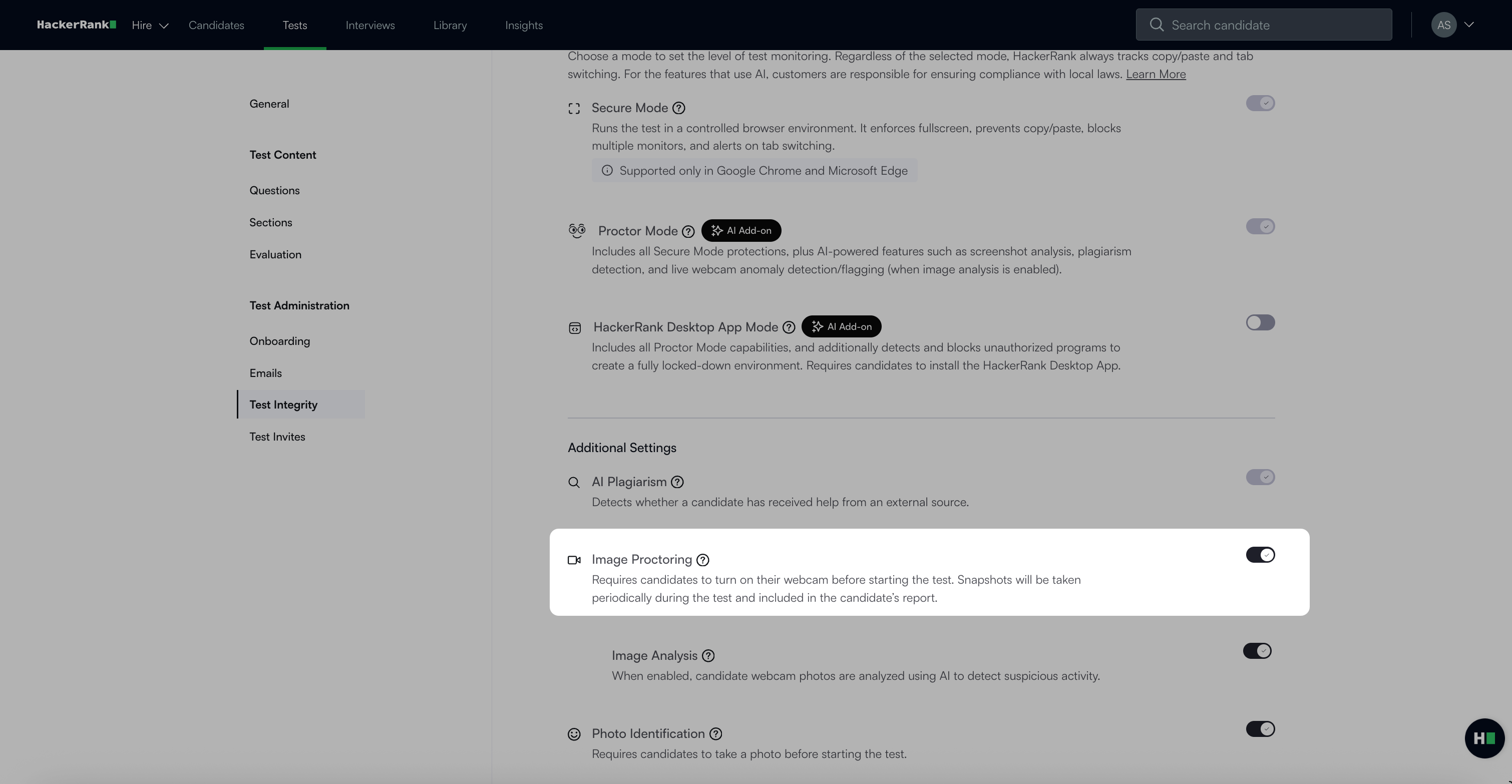
The Photo Identification feature in Test Integrity settings is disabled by default for all the tests.
Candidate Experience
When Photo Identification is enabled, the system captures a photo of the candidate before the test begins. To complete the identification process:
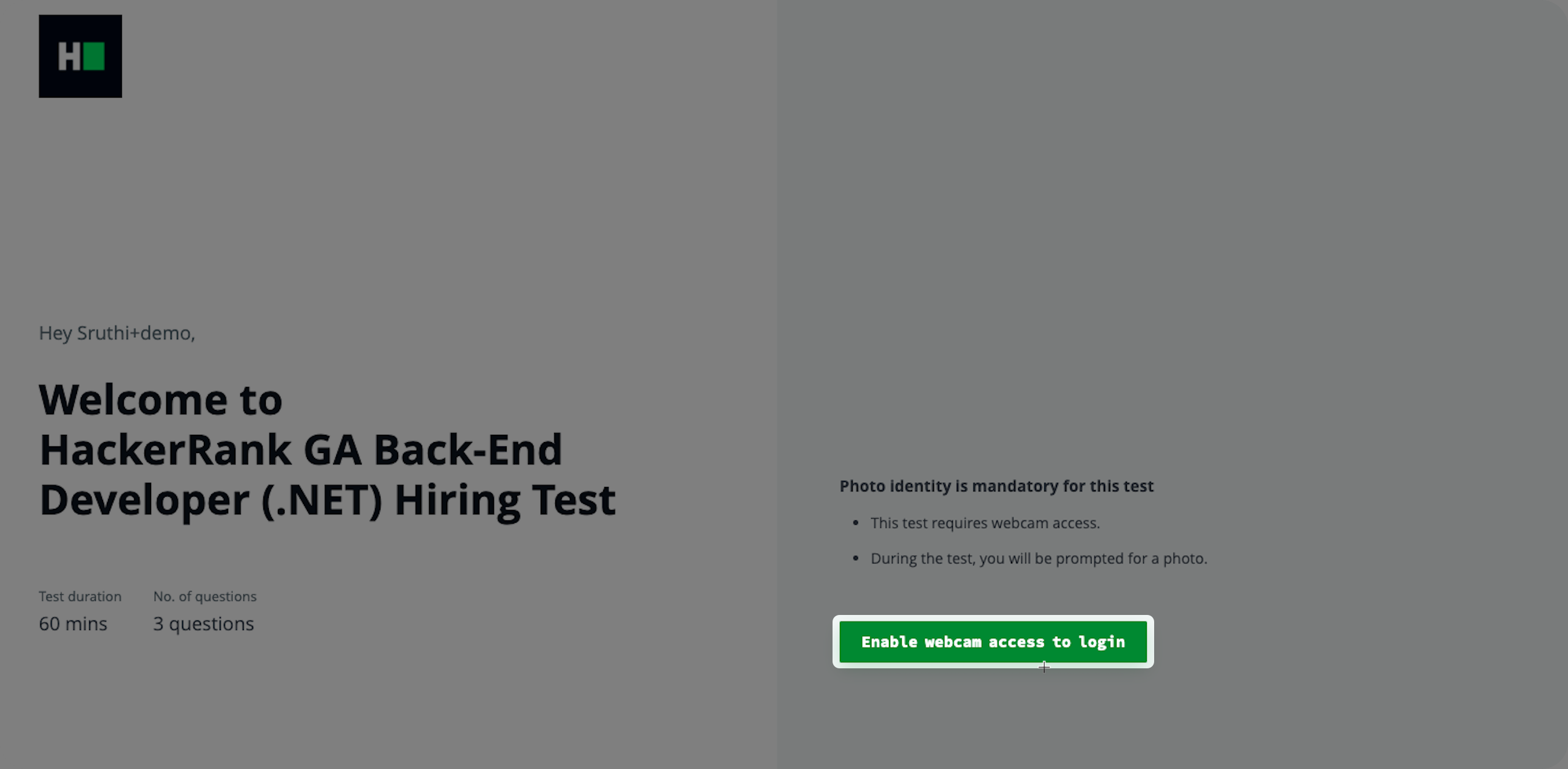
The candidate clicks the test link in the invite and lands on the test landing page.
The system prompts the candidate to allow webcam access. The candidate must grant permission and enter the required details to start the test.
Once inside the test, the system prompts the candidate to take their photo.
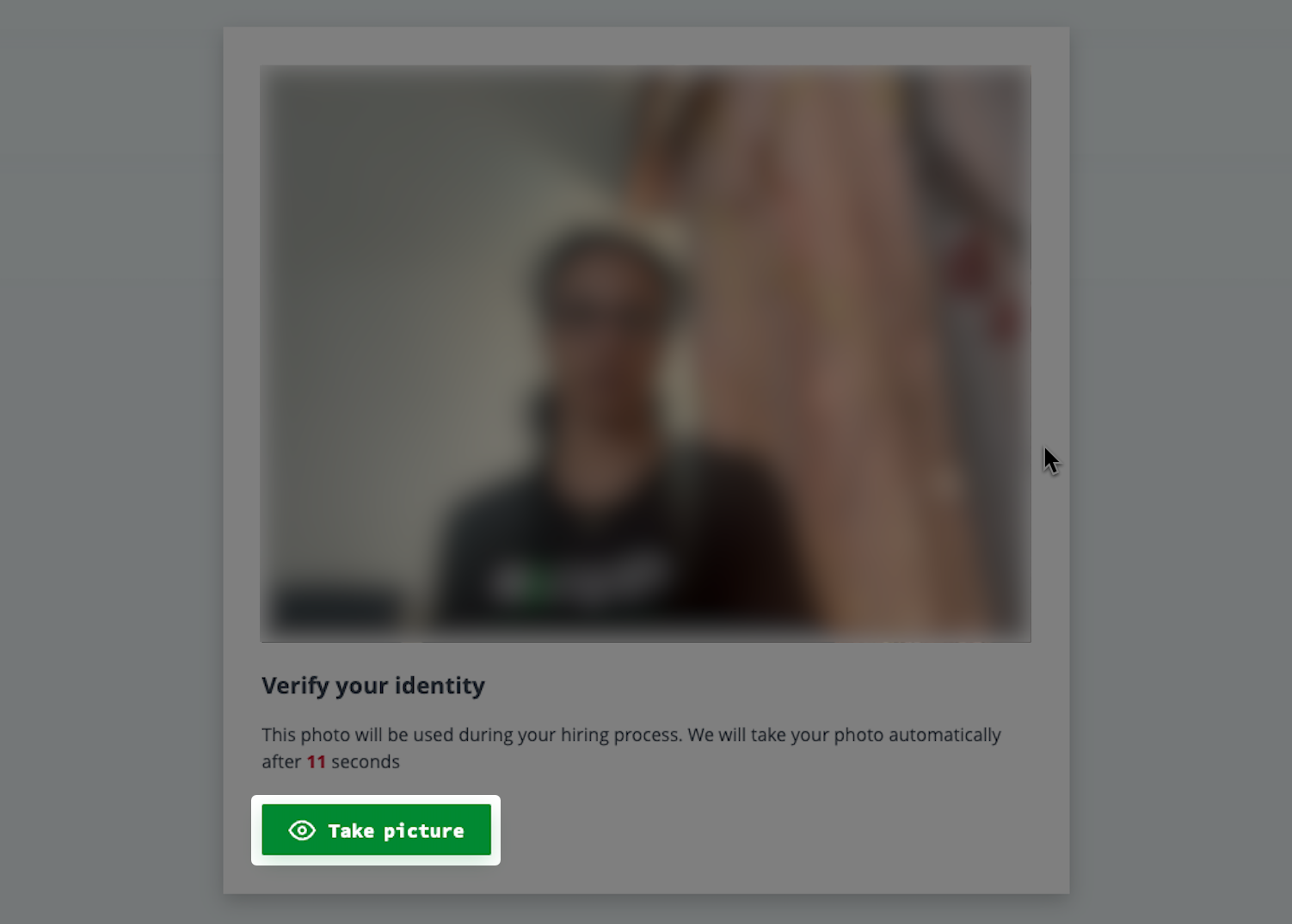
The test starts automatically after the candidate submits their photo.
Note: The system does not automatically validate or flag candidates based on the captured photo. The hiring team must manually verify the candidate's photo.
View Candidate Photo
To view the photo:
Open the test with Photo Identification enabled.
Select the candidate’s name to access the candidate summary report.
Go to the Attempt Activity tab.
Expand the Photo ID section to view the candidate’s photo.
Image Proctoring
The Image Proctoring feature captures images of candidates at one-minute intervals during the test. By default, this feature is disabled. This feature within the Test Integrity settings is disabled by default for all the tests to monitor suspicious activity during the test.
Candidate Experience
Before taking the test, the candidate is notified about Image Proctoring and to enable webcam access.
When the candidate enables webcam access, a message is displayed to the candidate outlining the conditions.
When the candidate clicks Continue, their image is captured periodically throughout the test duration or until the test is submitted.
Accessing Image Proctoring Results
To view the Image Proctoring results:
Open the test where Image Proctoring is enabled.
Select the candidate’s name to access the Candidate Summary report.
Go to the Attempt Activity tab.
Expand the Proctor section.
Multiple Monitor Detection
You can detect if an external monitor is connected to the candidate's device during an assessment. This can help identify potential cheating, as the use of multiple monitors can be a significant factor in decision-making.
This feature within the Test Integrity settings is disabled by default for all the tests.
Candidate Experience
HackerRank will detect and track the number of monitors that the candidate uses throughout the test. This feature is supported only on Edge, Chrome, and Chromium-based browsers. HackerRank will not prompt the candidate if they proceed with an unsupported browser.
Monitor Detection Logs in Test Reports
From the Timeline tab in the candidate report, you’ll be able to view the list of events, such as changes in the number of windows open throughout the duration of the test.

An additional column, Max Number of Monitors Detected, will appear in the CSV report, showing the highest number of monitors connected during the candidate's attempt.
Note: To view the details in the CSV, you must enable the report setting for Max Monitor Detected.
Webcam Switch Detection
The proctoring mechanism automatically detects if a candidate switches their webcam during an ongoing test. This feature helps recruiters and hiring managers identify potential suspicious activity and allows for further investigation into why the webcam was changed mid-test.
Review the information under the Timeline tab within a candidate test report and decide further course of action for the candidate.
Note: To view the details in the CSV, you will need to enable the report setting for Webcam Switch Detected.
Feature that uses AI to detect impersonation:
Image Analysis
The Image Analysis feature categorizes captured images during Image Proctoring based on flagged activity. Each flagged category displays up to five images for a quick review of suspicious activity. The Image Analysis feature is disabled by default under the Test Integrity section.
To enable Image Analysis, turn on Image Proctoring. This will unlock the option to toggle Image Analysis.
Agree and Enable the feature after reviewing the considerations.

Note: For more details, click the help icon or view the HackerRank NYC laws for AI. HackerRank’s AI-powered plagiarism solution has undergone an independent bias audit, ensuring compliance with the NYC AI Law.
Candidate Experience
When Image Analysis is enabled, candidates are prompted to allow webcam access. Upon launching the test, the candidate must consent to the proctoring and webcam access.
Note: Proctored tests are only supported on Chrome, Safari, Edge, and Firefox browsers.
Reviewing Suspicious Activity
To review a candidate’s suspicious activity:
Open the test and go to the Candidates tab.
Click on the candidate's name to view the Candidate Summary report.
Navigate to the Attempt Activity tab and expand the Image Analysis section.
The captured images are categorized based on the following:
Multiple Faces: Flags if two or more individuals appear in the same frame.
Secondary Faces: Detects if two or more candidates attempted the same test.
No Faces: Identifies when no face is detected.
Static Faces: Detects static image projections.
Image spoofing is the ability to detect if a candidate projects a static image during an ongoing test. This feature helps identify those candidates who try to use image spoofing software to pretend they are live while taking the test.
Reviewing Suspicious Activity in CSV Exports
Proctoring data is captured in the CSV report, with additional columns to help filter candidates based on suspicion severity, score, and reason. The columns include:
Proctor Activity Suspicion Severity
Proctor Activity Suspicion Score
Proctor Activity Reasons
The following examples help you to filter candidates based on their proctoring activities.
Example 1: If you are concerned only about highly suspicious candidates, use the Proctor Activity Severity column and filter out candidates marked as High.
Proctor Activity Suspicion Severity | Proctor Activity Suspicion Score | Proctor Activity Reasons |
High | 9 | Multiple faces detected, No faces detected |
Medium | 7 | Multiple faces detected |
Medium | 5 | Multiple faces detected |
Example 2: If you are ok with moving ahead with candidates flagged for reasonable suspicious activity, use the Proctor activity suspicion score column to filter candidates appropriately.
Proctor Activity Suspicion Severity | Proctor Activity Suspicion Score | Proctor Activity Reasons |
High | 9 | Multiple faces detected, No faces detected |
Medium | 7 | Multiple faces detected |
Medium | 5 | Multiple faces detected |
High Suspicion: Scores of 8-10 indicate high suspicion, such as multiple or no faces detected.
Medium Suspicion: Scores of 5-7 indicate moderate suspicion, like multiple faces or potential spoofing.
Low Suspicion: Scores below 5 indicate no significant issues.
Note: When progressing candidates are flagged as Medium, it is recommended that further assessments be conducted to ensure that no cheating occurred in the previous rounds.